![[RSS]](/static/img/feed-icon-14x14.2168a573d0d4.png) Conservancy Blog
Conservancy Blog
2024 End-of-Year Fundraiser Succeeds: over $480k to support software freedom
by on January 16, 2025
We thank both donors who offered this historic $204,877 match & those who gave to help to exceed the challenge
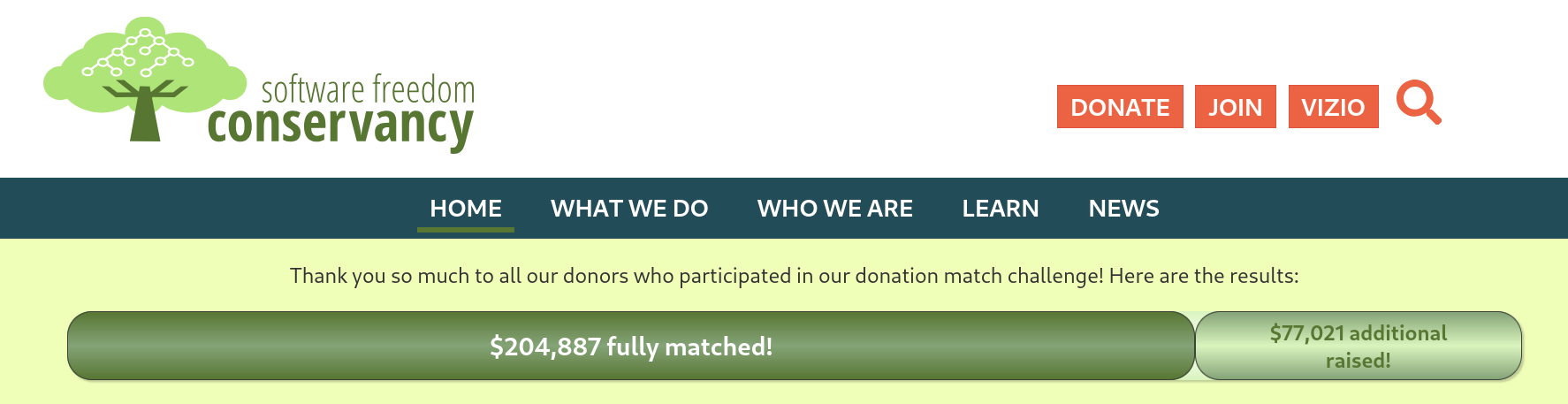
In late November, SFC, with the help of a group of generous individuals who pledged match gifts large and small, posted a huge challenge to our donors. We were so thankful for the donors who came together to offer others a match challenge of $204,877 — which was substantially larger than any of our match challenges in history.
Donors heard our ask, and we were even more thankful of all the donors who responded. Toward the end, we were so overwhelmed by last minute response that we were tabulating updates by hand. We saw so many donors who had already given coming in for another $10, $50 or $100 to get us there. We made the match primarily because of the hundreds of small donors who came in with Sustainer amounts, and we thank those small donors so much for often doing a bit extra: so many of you hit the $512 and even the $1024 button instead of the minimum of $128. It means so much to us when we see a donor who gave $128 in 2023 double their donation for 2024 — you all made this match challenge succeed. We also so appreciate the donors who, despite experiencing financial challenges, gave smaller amounts when it was a stretch for them to give at all.
Most surprising of all, an anonymous donor who in the past has made a very large donation around the time of FOSDEM came in early this year. That donation bursts us right through our status bar and puts us well over. We've raised over $475,000 this season, which is now reflected on our fundraiser status bar. (We're still tabulating and entering the paper checks and ACH/wire transactions that came during the final days of the fundraiser, so the number may soon increase even more!)
We are truly humbled. Every year, our staff is working tirelessly through the holiday season to make sure we balance our work and fundraising. Every dollar you all give us is noticed and appreciated, and gets us there, step by step.
SFC does receive some grants and corporate sponsorship for which we are also grateful, but the bulk of our funding comes from individual donors, like you. Fundraising is (sometimes annoyingly) mandatory work that as a small staff we must do in addition to our normal work. Nevertheless, it's a simple fact that the more you donate, the more program activity we can do. In essence, you make our important work for software freedom and rights.
Karen Sandler interviews Cory Doctorow
by on January 15, 2025
Our Executive Director Karen Sandler recently sat down with Cory Doctorow to talk about software right to repair, the utility and history of DMCA exemptions, and some of the differences between the way laws take effect in different places around the world. Doctorow is widely known for his speculative fiction touching on issues of technology, activism, and post-scarcity economics. We were so excited for this conversation, many on SFC staff are fans and had a great time preparing for the conversation.
Covering a range of topics, it was great to hear from Cory about how proprietary platforms can actually lead to conversations with loved ones about interoperability. Of particular note was a discussion about the similarities to the accessibility rights movement. Interoperability and accessibility are fundamental rights that technology should empower us to have, but often times we need to advocate and fight for those rights.
If you run out of things you can do with code, there's nothing wrong with mounting a big normative campaign. If the norms aren't doing it for you...
With a good appreciation of history combined with a forward looking eye Doctorow's unique perspective sheds light on how the free software movement can be more open to availing itself to the wider public. We look forward to a future where more people are brought into the conversations and issues that today's technology forces us to reckon with.
Karen talked about the potential of software freedom and in particular the opportunities inherent in all copyleft licenses to completely change the way ordinary people experience technology that impacts them. She talked about the concrete and incremental work Software Freedom Conservancy does to move the needle towards ethical technology.
Thanks to Cory for sitting down with Karen and having a great conversation that we hope inspires you as much as us to look to the future with eagerness and energy for change!
PS: Today is the last day of our fundraiser, so if you like content like this, please donate now to support us in making things like this happen!
Embroidery and resilient software freedom in 2025
by on January 6, 2025
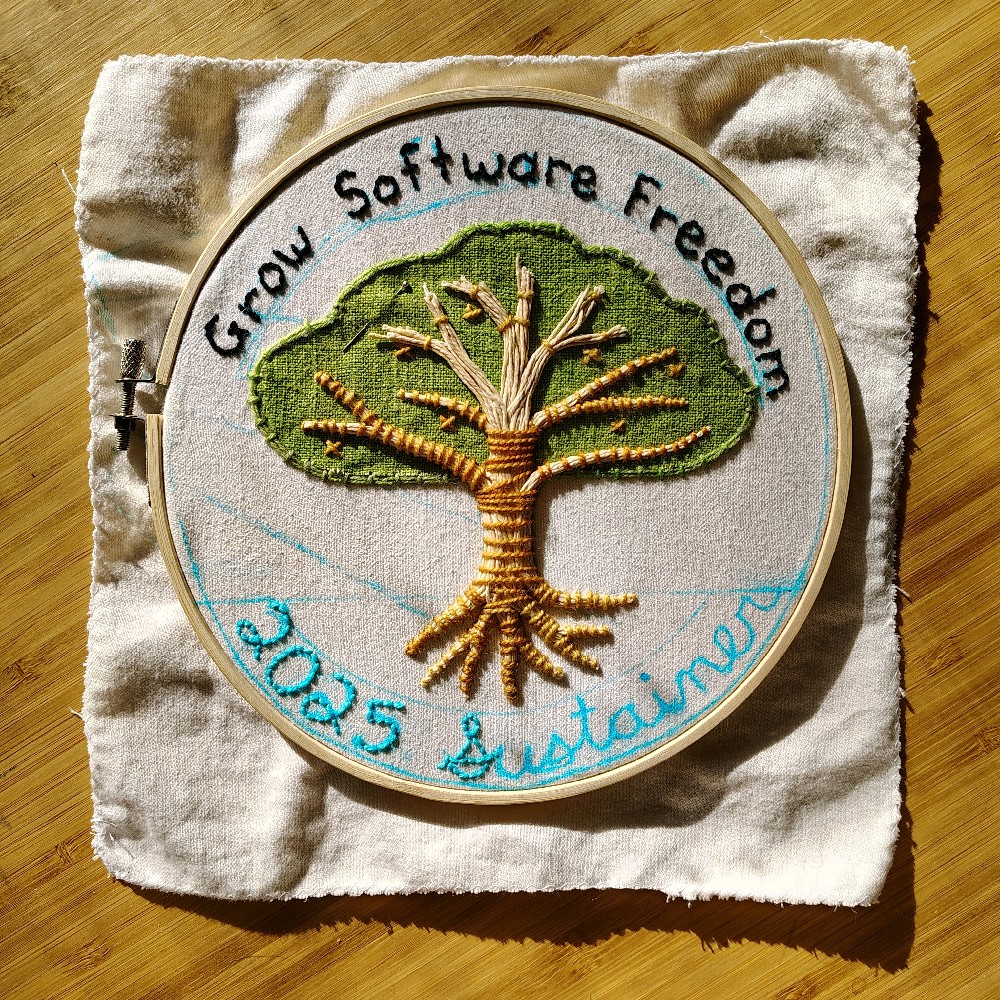
CC-BY-NA 4.0 Sage Sharp
I spent most of 2024 recovering from a spine injury after a car accident. I’d love to share my new insight into free software accessibility, and how both free software and embroidery helped me build resiliency. I’ve been working on a special embroidery that I’ll send to a donor who gives to Software Freedom Conservancy on January 8. We hope if you are able to give you’ll consider donating!
Outreachy Team AMA
Please join me on January 8 for a Q&A session with the SFC staff and contractors who run the Outreachy internship program. After the Outreachy organizer Q&A, join me for a crafting session while I work on the SFC logo embroidery.
There will be two Q&A sessions with the Outreachy team to accommodate time zones. You can join us on BigBlueButton at the times below (information is also in the attached .ics files):
First chat on Wednesday:
- Wednesday 8 January 2025 at 9AM (09:00) US/Eastern (-0500)
- Wednesday 8 January 2025 at 6AM (06:00) US/Pacific (-0800)
- Wednesday 8 January 2025 at 3PM (06:00) Europe/Central (+0100)
- date -d "2025-01-08 14:00 UTC"
Second chat on Wednesday:
- Wednesday 8 January 2025 at 9PM (09:00) US/Eastern (-0500)
- Wednesday 8 January 2025 at 6PM (06:00) US/Pacific (-0800)
- Thursday 8 January 2025 at 1PM (13:00) Australia/East (+1100)
- date -d "2025-01-09 02:00 UTC"
My healing journey
In February 2024, my car was rear-ended. The impact damaged the nerves from my shoulder to my hand.
I had pain and tingling in my fingers for 6 months. Everything I touched felt like picking up a cactcus.
It was painful to type on a keyboard. Touching my phone, either to swipe or type, hurt.
This chronic pain made it hard to do my normal work tasks as Software Freedom Conservancy’s Senior Director of Diversity and Inclusion, and an organizer for Outreachy internships. Most free software communication happens via email or text chat. Which meant a whole lot of very painful typing for me.
Luckily, free and open source software helped me find a more accessible way to work. I dreaded looking for accessibility software because I knew it’s usually both expensive and proprietary. I was so excited to find speech to text free software like vosk for the Linux desktop. For my phone, I found sayboard, a speech to text Android keyboard that uses vosk.
Free software allowed me to switch away from using my hands to write, and towards using my voice to write. I wrote this email using those tools. I am so grateful to the free software developers who helped me avoid hand and shoulder pain.
Accessibility in FOSS
My injury also gave me a new perspective on the gaps in software accessibility best practices. Very few free software projects offer options to accommodate people who have pain whenever they touch a screen, use a keyboard, or click a mouse button.
Free software developers rarely think about how many actions it takes to do a particular task. How many mouse clicks does it take to find information on a website? How many phone screen touches does it take to use that new feature?
When I have to go through five software actions to do a task, my brain translates each mouse click, phone screen touch, and keyboard press into feeling like a needle is poking my finger. Extra actions to complete a task are literal pain points for me.
I encourage other free software developers to explore how many touches, clicks, or key presses it takes to do a common task. My fellow Outreachy organizer, Anna e só, mentioned there is a whole field of Human-Computer Interaction research around minimizing software task overhead.
I encourage other free software developers to study their project’s gulfs of evaluation and execution. Identifying the extra actions it takes to execute a task may help you understand how software contributes to chronic hand pain. Anna recommends reading the book “The Design of Everyday Things” by Donald A. Norman to get started learning about this field research.
Community support and accommodations
Even with somewhat improved free software accessibility, I still needed time to rest and recover. SFC staff and the Outreachy team helped me reassign tasks that required a lot of typing or mouse movement. They encouraged me to find verbal and audio-based work. I also shared knowledge and processes so that any team member could do critical tasks.
I am so grateful to SFC and the Outreachy team for their flexibility and accommodation of my short term disability.
While my body was healing, I thought a lot about the right to repair, both for software and for physical objects. Why do we decide an object is beyond repair, and must be replaced by something expensive and new? Why do companies put out products that easily break physically, or will become obsolete or insecure due to a lack of software updates?
In a world of shiny fragile tech toys and easy to consume fast fashion, I felt out of place. I felt like my healing body would be viewed as imperfect, broken, and disposable. I worried that opening up about my invisible disabilities would cause people to view me as needing to be replaced.
My identity as a free software contributor was so dependent on using my hands. My outdoor hobbies involved climbing over rocks or gripping a walking stick for a long time, both of which caused hand and back pain. Who was I, if I could not use my hands in ways I was used to?
Resiliency and Embroidery
While I was healing, I needed to be more gentle with my physical self. I also wanted a hobby that would help me rebuild my hand dexterity and nerve sensation. So I took up embroidery.
When it came time for the SFC fundraiser, I knew I couldn’t be on social media as much because it would cause additional hand and back pain to be so online. Instead I decided to create an embroidered art piece that would encourage people to donate to Software Freedom Conservancy.
Other SFC staff were excited about my embroidery project, and crafting became a theme for SFC’s fundraiser. SFC’s yearly post card features SFC’s tree logo re-imagined as a cross-stitch. We also created a special t-shirt design (available if you become a sustainer ) this year that features a work-in-progress cross-stitch of SFC’s logo. In both free software and crafting projects, there is always something to more improve or work on.
I’m so excited to send my embroidered art to an SFC donor. My embroidery is an artistic take on Software Freedom Conservancy’s tree logo. It features the words ‘Grow Software Freedom’, and ‘2024 Sustainer’.
A tree cannot thrive without good water and sunlight. SFC cannot thrive without your support. I encourage you to donate today at https://sfconservancy.org/sustainer/.
Donate for Embroidery
Your donation to Software Freedom Conservancy will help us grow software freedom together.
My embroidered art will go to the top donor SFC’s fundraiser, from the time you receive this email until end of day (AOE) on January 8th. If the top donor doesn’t want it, the art will go to a random donor, including anyone who donated from the start of Conservancy’s fundraiser through January 8th.
This means even if you can only give a smaller amount to support Conservancy, there is still a chance you may receive this SFC art. Every donation to SFC helps us sustain software freedom!
I hope you will take heart in my recovery journey. If it inspires you, please use that energy to support software freedom, especially the right to repair and accessibility.
I encourage you to donate to Software Freedom Conservancy to build the resilient future free software needs.
--
Sage Sharp
Senior Director of Diversity and Inclusion at Software Freedom Conservancy
Cultural Change Agent at Outreachy
Kuleana and software freedom for the future
by on December 23, 2024
Pono and Meredith in Hawai'i - CC-BY-NA 4.0 Pono Takamori
During the holiday season I really want to share with you some thoughts on why software freedom is so important to me. Please donate during our fundraiser (and have you donation doubled from our matchers!). Also please see the note at the bottom about 2 Q&A sessions we’ll be having on December 27th and 30th!
My name is Pono, a name my native Hawaiian grandmother gave me. In Hawaiian we have a word: kuleana. A duty to take care of the land and the people around you given your own gifts and abilities. It’s been an important concept to me to guide me and share my passions and desires for a better world with the community around me. I came to Software Freedom Conservancy first as a Sustainer and activist, and then years later an employee. Software Freedom is an interesting area to think about place, because the digital world sometimes feels like an astral plane, so distant from our everyday lives. But the reality is that we can inhabit the physical world and digital world at the same time. Whether it’s liberating farming equipment so that we can repair the software on tools vital for food production or making sure that the internet connected devices in our homes are not spying on us, our stewardship for the Earth and for the digital spaces we occupy are not distinct but intertwined.
My wife and I are expecting our first child soon. We’re so excited for the future and how the three of us will grow and experience the world together. And while software freedom certainly wasn’t the first thing on our minds in this situation, we’ve already encountered baby gear that is internet connected and has moved to subscription model for existing features (this article from The Register talks about it as well as the letter we signed to the FTC advocating against such technology). It’s frustrating the many ways that our technology is dictated to us, when it is from our own labor that all this technology is created in the first place [footnote]. What does software freedom look like to someone growing up in a world filled with proprietary cloud based software, an increasing surveillance state, and corporations seeking to lock you in the their walled gardens?
Working for Software Freedom Conservancy has been amazing to work with community to build our collective future. We focus on protecting technological rights that corporations continually belittle and seek to undermine. Working with such an incredibly passionate and small team is something that makes advocating for software freedom feel good. Our activism, while sometimes driven to fight back against unchecked power, has it’s roots in the joy and liberation of programming and cooperation of our digital activities. It’s a long road ahead, but we must remember that there is joy to be had along the way.
I’m sure by wishing my daughter has an interest in computers, she will wind up finding her joy somewhere else. But isn’t that what we want? Regardless of technical proficiency or interest, we want to guarantee rights for all people. My kuleana is knowing that I’ve been given abilities and an interest in computing; I have a responsibility to others to make sure they are afforded the same rights and privileges I’ve attained.
I’m so thankful for the opportunity to share my story and why I think software freedom is a necessary (if not sufficient) condition for human liberation. It's my humble ask to support our organization you spread the word and tell a friend or family member about what we do. But if you are able to give this season, your contribution will be doubled during our fundraiser :)
While the annual sustainership level is $128/year, you can make monthly donations and get all the benefits of sustaining SFC for lightly less (at just $10/month)!
We’d also like to invite you to a Q&A with our Executive Director Karen Sandler and Policy Fellow Bradley M. Kuhn on the evening of December 27th and morning of December 30th. Use the commands below to find your local time.
$ date -d "2024-12-27 14:00 UTC"
$ date -d "2024-12-31 02:00 UTC"
Join us in #conservancy on libera.chat or our XMPP channel at those times for the BigBlueButton link. Can’t wait to see you!
Maholo nui loa,
— Daniel Sean Pono Takamori
footnote: The Luddites get a bad rap, but they were the skilled laborers who fought against technology replacing them in a way that's very reminiscent to our own movement. I highly recommend Brian Merchant's book "Blood in the Machine: The Origins of the Rebellion Against Big Tech"
Next page (older) » « Previous page (newer)
1 2 3 [4] 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70
